Views: 36
Enumeration
Nmap scan
C:\home\zybersec> nmap -sC -sV -p- -A -T5 172.16.1.107 -oN prime1.txt
Starting Nmap 7.93 ( https://nmap.org ) at 2023-04-30 07:53 CEST
Nmap scan report for 172.16.1.107
Host is up (0.0017s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 8dc52023ab10cadee2fbe5cd4d2d4d72 (RSA)
| 256 949cf86f5cf14c11957f0a2c3476500b (ECDSA)
|_ 256 4bf6f125b61326d4fc9eb0729ff46968 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: HacknPentest
|_http-server-header: Apache/2.4.18 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 29.21 secondsExpand
Gobuster
C:\home\zybersec> gobuster dir -u 172.16.1.107 -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt -x .php,.txt,.bak,.conf
===============================================================
Gobuster v3.5
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://172.16.1.107
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.5
[+] Extensions: php,txt,bak,conf
[+] Timeout: 10s
===============================================================
2023/04/30 08:05:36 Starting gobuster in directory enumeration mode
===============================================================
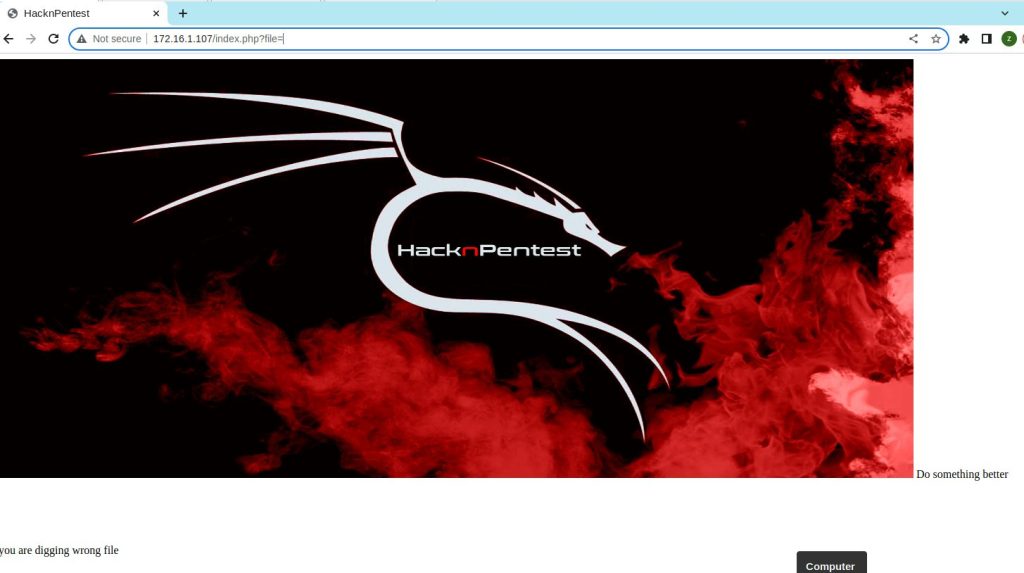
/index.php (Status: 200) [Size: 136]
/.php (Status: 403) [Size: 291]
/image.php (Status: 200) [Size: 147]
/wordpress (Status: 301) [Size: 316] [--> http://172.16.1.107/wordpress/]
/dev (Status: 200) [Size: 131]
/javascript (Status: 301) [Size: 317] [--> http://172.16.1.107/javascript/]
/secret.txt (Status: 200) [Size: 412]
/.php (Status: 403) [Size: 291]
/server-status (Status: 403) [Size: 300]
Progress: 1037618 / 1038220 (99.94%)
===============================================================
2023/04/30 08:09:25 Finished
===============================================================Expand
Gobuster – wordpress folders scan
C:\home\zybersec> gobuster dir -u 172.16.1.107/wordpress -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt -x .php,.txt,.bak,.conf
===============================================================
Gobuster v3.5
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://172.16.1.107/wordpress
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.5
[+] Extensions: txt,bak,conf,php
[+] Timeout: 10s
===============================================================
2023/04/30 08:11:13 Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 301]
/index.php (Status: 301) [Size: 0] [--> http://172.16.1.107/wordpress/]
/wp-content (Status: 301) [Size: 327] [--> http://172.16.1.107/wordpress/wp-content/]
/wp-login.php (Status: 200) [Size: 3281]
/license.txt (Status: 200) [Size: 19935]
/wp-includes (Status: 301) [Size: 328] [--> http://172.16.1.107/wordpress/wp-includes/]
/wp-trackback.php (Status: 200) [Size: 135]
/wp-admin (Status: 301) [Size: 325] [--> http://172.16.1.107/wordpress/wp-admin/]
/xmlrpc.php (Status: 405) [Size: 42]
/.php (Status: 403) [Size: 301]
/wp-signup.php (Status: 302) [Size: 0] [--> http://172.16.1.107/wordpress/wp-login.php?action=register]
Progress: 1038168 / 1038220 (99.99%)
===============================================================
2023/04/30 08:15:11 Finished
===============================================================Expand
Enumerating webcontents

WordPress Installation
WPScan
C:\home\zybersec> wpscan --url http://172.16.1.107/wordpress -e
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.22
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[i] It seems like you have not updated the database for some time.
[?] Do you want to update now? [Y]es [N]o, default: [N]Y
[i] Updating the Database ...
[i] Update completed.
[+] URL: http://172.16.1.107/wordpress/ [172.16.1.107]
[+] Started: Sun Apr 30 08:13:28 2023
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.18 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://172.16.1.107/wordpress/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://172.16.1.107/wordpress/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://172.16.1.107/wordpress/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://172.16.1.107/wordpress/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.2.2 identified (Insecure, released on 2019-06-18).
| Found By: Rss Generator (Passive Detection)
| - http://172.16.1.107/wordpress/?feed=rss2, <generator>https://wordpress.org/?v=5.2.2</generator>
| - http://172.16.1.107/wordpress/?feed=comments-rss2, <generator>https://wordpress.org/?v=5.2.2</generator>
[+] WordPress theme in use: twentynineteen
| Location: http://172.16.1.107/wordpress/wp-content/themes/twentynineteen/
| Last Updated: 2023-03-29T00:00:00.000Z
| Readme: http://172.16.1.107/wordpress/wp-content/themes/twentynineteen/readme.txt
| [!] The version is out of date, the latest version is 2.5
| Style URL: http://172.16.1.107/wordpress/wp-content/themes/twentynineteen/style.css?ver=1.4
| Style Name: Twenty Nineteen
| Style URI: https://wordpress.org/themes/twentynineteen/
| Description: Our 2019 default theme is designed to show off the power of the block editor. It features custom sty...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.4 (80% confidence)
| Found By: Style (Passive Detection)
| - http://172.16.1.107/wordpress/wp-content/themes/twentynineteen/style.css?ver=1.4, Match: 'Version: 1.4'
[+] Enumerating Vulnerable Plugins (via Passive Methods)
[i] No plugins Found.
[+] Enumerating Vulnerable Themes (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:03 <===============================================================================================================> (498 / 498) 100.00% Time: 00:00:03
[+] Checking Theme Versions (via Passive and Aggressive Methods)
[i] No themes Found.
[+] Enumerating Timthumbs (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:20 <=============================================================================================================> (2575 / 2575) 100.00% Time: 00:00:20
[i] No Timthumbs Found.
[+] Enumerating Config Backups (via Passive and Aggressive Methods)
Checking Config Backups - Time: 00:00:01 <================================================================================================================> (137 / 137) 100.00% Time: 00:00:01
[i] No Config Backups Found.
[+] Enumerating DB Exports (via Passive and Aggressive Methods)
Checking DB Exports - Time: 00:00:00 <======================================================================================================================> (71 / 71) 100.00% Time: 00:00:00
[i] No DB Exports Found.
[+] Enumerating Medias (via Passive and Aggressive Methods) (Permalink setting must be set to "Plain" for those to be detected)
Brute Forcing Attachment IDs - Time: 00:00:03 <===========================================================================================================> (100 / 100) 100.00% Time: 00:00:03
[i] No Medias Found.
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:00 <=================================================================================================================> (10 / 10) 100.00% Time: 00:00:00
[i] User(s) Identified:
[+] victor
| Found By: Author Posts - Display Name (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Sun Apr 30 08:14:14 2023
[+] Requests Done: 3444
[+] Cached Requests: 8
[+] Data Sent: 1003.956 KB
[+] Data Received: 13.307 MB
[+] Memory used: 298.168 MB
[+] Elapsed time: 00:00:45
Expand