Posted inVulnLAB Purple Teaming RED TEAM
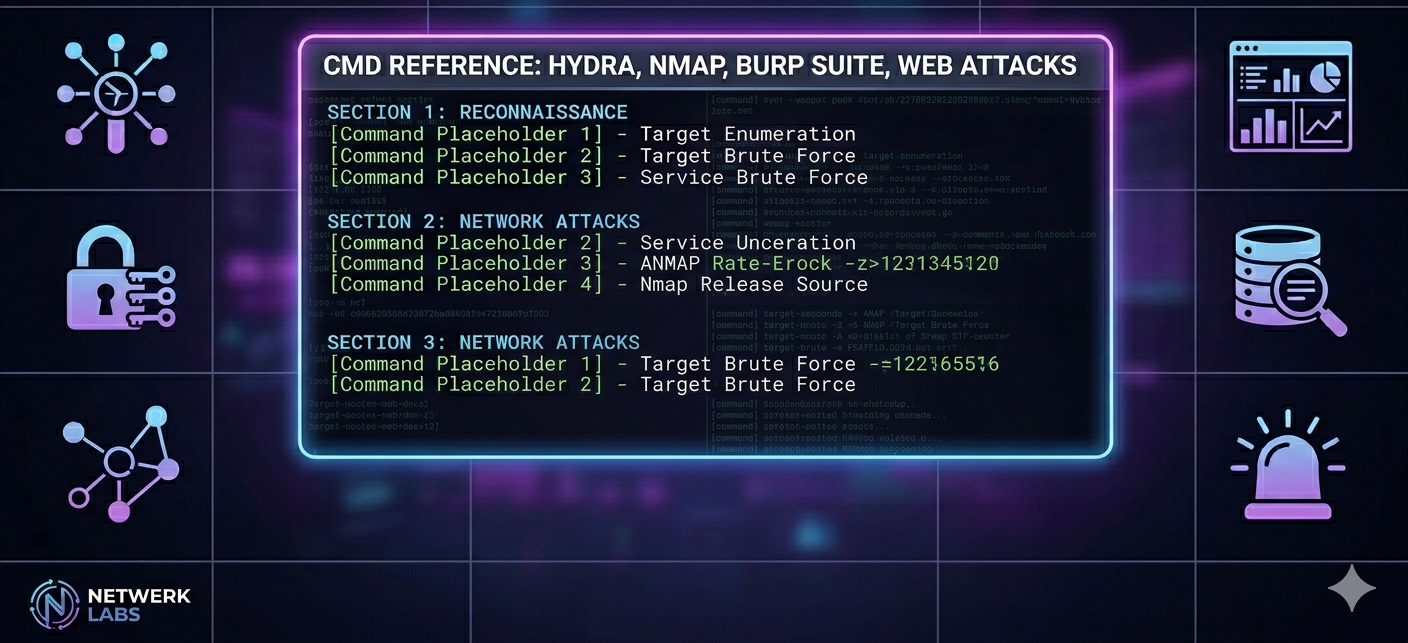
Nmap Cheat Sheet
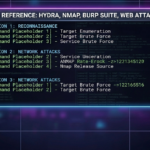
Nmap Cheat Sheet nmap — cheat sheet Network Mapper · Comprehensive Command Reference 🎯 Target Specification 8 nmap 192.168.1.1·Scan a single IP nmap 192.168.1.1-254·Scan IP range nmap 192.168.1.0/24·Scan CIDR subnet…